Author: e-ukiyo
TryHackMe Gotta Catch’em All! Write-Up
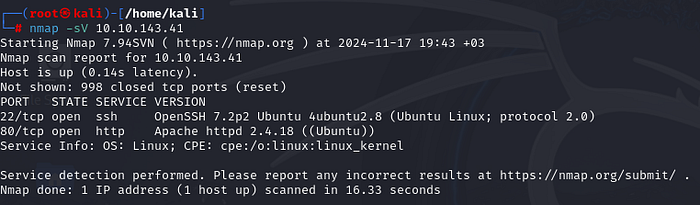
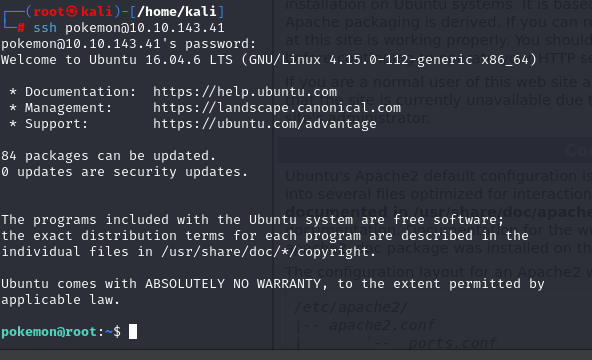
Deploying the machine and my target ip is 10.10.143.41
First off all scanning the machine with nmap and I found 22 and 80 ports are open.
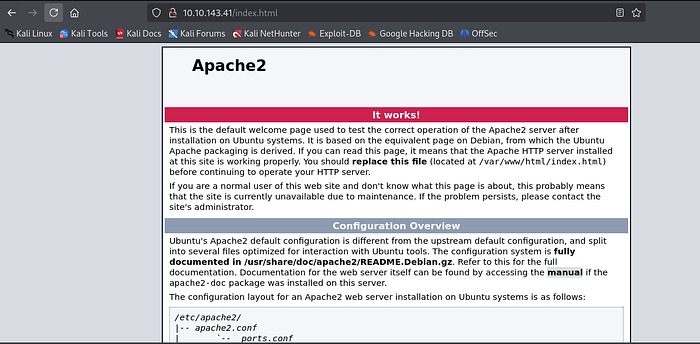
Then doing a gobuster scan but nothing interesting.

Visit the default page and there is nothing we can do :/
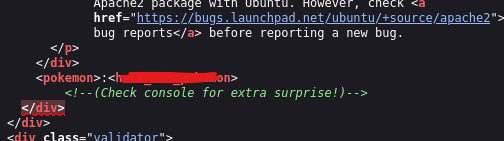
So, take a look the page source and finally found something. It’s probably ssh nickname and password.
Yeah it is work!
In desktop there is a zip file. Unzip it and there is the grass-type pokemon.
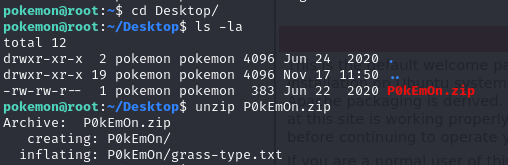
We can read it with cat command but its encrypted with hex.
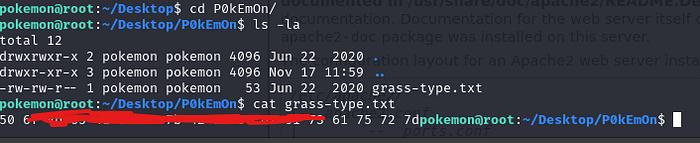
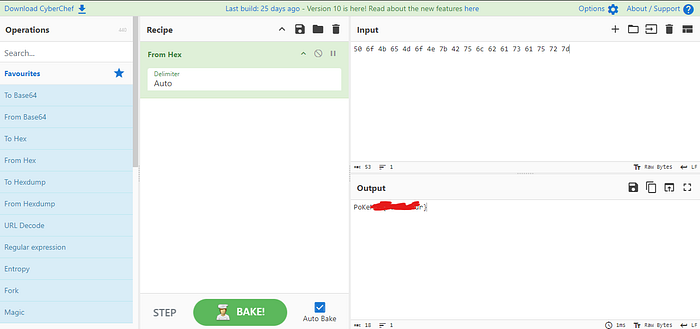
I deceode it with cyberchef and here is the grass-type pokemon flag.
I search for the water-type pokemon but i cant see. So search with locate command and here is txt file. But its encrypted too.

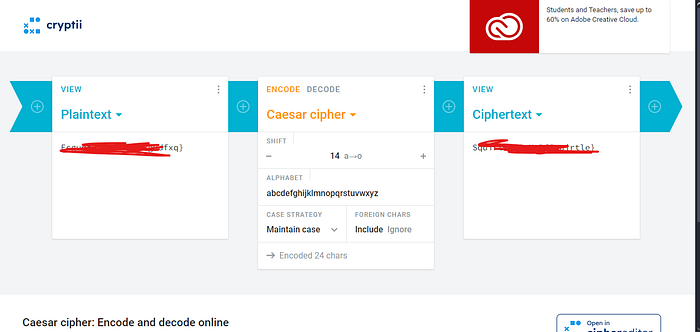
It’s look like caesar cipher cryptography algorithm so i use this decoder. And here is the water-type pokemon flag.
Then I search other files and in videos files I found something.
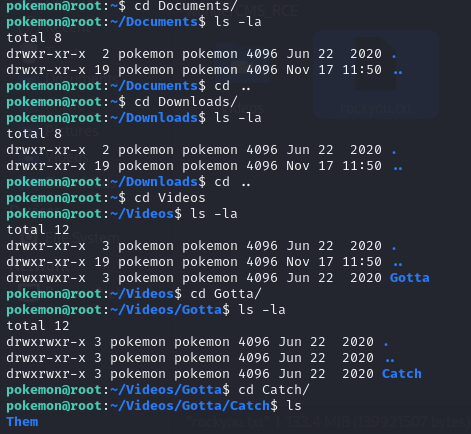
There is a password for ash user.
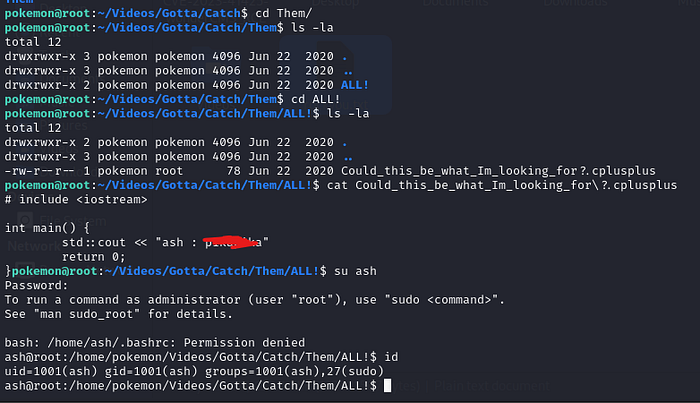
Check with sudo -l command and we can see (ALL : ALL) ALL .
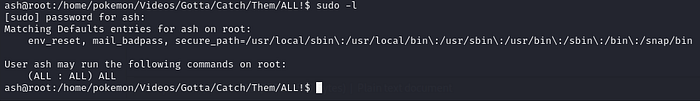
This mean is if you type sudo su, you can be root with any password.
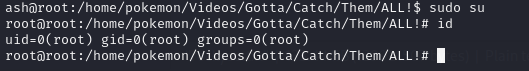
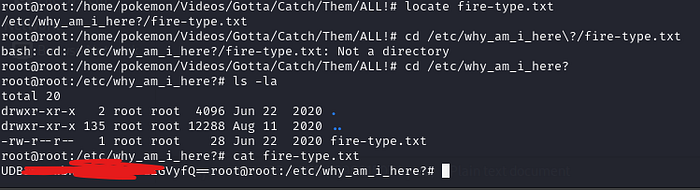
Okay we are root now. Find the fire-type pokemon with locate command. But this file encrypted too :( It’s look like crypted with base64 so I use cyberchef again. And here is the fire-type pokemon flag.
Finally we can read the roots favorite pokemon.
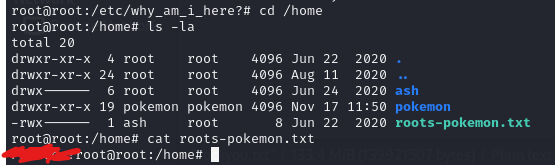
We are done!!!